As mobile becomes the primary operational channel for modern enterprises – a dominance fueled by a massive generational shift in user behavior – the threat landscape is expanding at an equally aggressive pace. While mobile ecosystems are in many ways architecturally superior to legacy systems, cybercriminals are increasingly setting their sights on these high-value targets. App stores are seeing a surge in fraudulent software and "Vapor apps" that morph into malware post-installation, contributing to a staggering 38% jump in Android-specific threats.
This new reality dictates that modern security must move far beyond the firewall and the centralized server. Today, the most critical vulnerabilities often exist in the "last inch" of the user experience – the physical interactions governed by NFC, Bluetooth, and the local device environment. To build a truly resilient product, leadership must pivot from merely protecting data in transit to securing the user’s physical proximity and their immediate digital surroundings. The ultimate goal? Ensuring that every tap, wave, and connection remains a trusted and untampered exchange.
Resilience strategy: Mobile vs. desktop & the trust hierarchy
To build a resilient app in 2026, we must look beyond the screen. Mobile devices are sensor-rich environments that offer unique ways to protect users, provided we leverage their architecture correctly. In some aspects, they are much more secure than browsers; in others, they require additional security layer.
Mobile advantage: Why mobile is your strongest ally
While we often focus on risks, the mobile ecosystem offers built-in security features that outperform traditional desktops. By utilizing these, you empower your users with a fortress in their pockets.
| Feature | The Mobile Strength | The Desktop Gap |
|---|---|---|
| Sandboxing | Privacy by Design: Every app lives in a dedicated "vault." This isolation ensures that even if one app is compromised, your app’s data remains shielded. | Open Access: Desktop processes often share system-level access, making it easier for a single breach to spread. |
| Identity | Seamless Trust: Native biometric authentication (FaceID, Liveness Detection) allows users to prove their identity instantly and securely without typing a single password. | Friction & Risk: Heavy reliance on passwords and managers, which are vulnerable to keyloggers. |
| Hardware Roots | Verified Integrity: Mobile hardware uses "Secure Enclaves" to store cryptographic keys, making it nearly impossible for unauthorized software to steal credentials. | Software-Dependent: Desktops often lack standardized hardware-level protection for sensitive keys. |
Designing security in 2026 is like choosing the right attire for the occasion. In the world of mobile R\&D, success depends on precisely matching technological rigor to the actual risk posed by a specific feature. Understanding your product's "Trust Profile" allows you to implement controls that, instead of being an irritating barrier, become a hallmark of quality and professionalism for the user.
In the critical category, covering FinTech and mobile commerce app security, "silent protection" has become the standard. How to secure a banking app or an mcommerce app in 2026? Users expect the app to act as a guardian in the background; mechanisms like RASP (Runtime Application Self-Protection) and certificate pinning are the foundations that secure their assets without interrupting the flow of the transaction.
Meanwhile, in the loyalty sector, we are discovering a new value: loyalty points are the new digital currency. Even a simple mention of secure data storage sends a clear signal to the customer that you value their engagement as much as their cash. And as self-service features gain momentum, securing the scanning process will become another crucial point.
Beyond the OWASP mobile top 10: Practical security application examples
Based on the OWASP MASVS v2.1.0 document, here are 10 key practices for mobile application security:
- Secure sensitive data
- Prevent data leakage.
- Employ strong cryptography.
- Manage keys professionally.
- Use secure auth protocols.
- Secure all network traffic.
- Validate platform integrity.
- Sanitize all untrusted inputs.
- Enforce mandatory updates.
- Minimize data access.
The good practices we gathered based on our project experiences and research dive deeper into modern mobile app security, incorporating the most recent technologies like AI agents and increasing security threats.
Whatever kind of app you are securing, the 2026 vision is clear: by minimizing unnecessary permissions and maximizing data protection, you are winning long-term customer trust, which is the most valuable capital in today's digital ecosystem.
Mobile application security best practices: How to secure mobile app while maximizing user comfort
1. Seamless identity verification via gov-tech integration
Does a red flag go up in your mind when an app asks you to verify your identity by taking a photo of your ID? It’s a natural reaction, and quite a healthy one, considering how many scams begin with harvesting personal information through a camera lens.
For a founder, this creates a classic friction point: high-stakes products in FinTech or HealthTech require a rigorous application security verification standard, yet demanding manual uploads often leads to massive user drop-off. The challenge lies in merging ironclad security with a user experience that doesn't trigger a flight response.
Instead of forcing users to play the role of a semi-professional photographer, the most forward-thinking products are leveraging "magic" verification through national digital ID systems like mObywatel or other government-backed digital wallets. This approach allows a user to authenticate via their own trusted government app using biometrics, completing the process in a single click. By moving away from raw ID photos, you eliminate the liability of storing sensitive images while ensuring the highest tier of data protection through officially verified credentials.

Orchestrating the handshake between trust and transparency
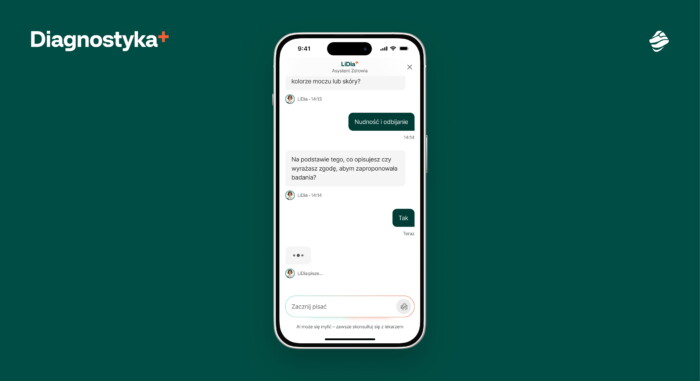
It is important to recognize, however, that government-led digital IDs aren't universal yet. In markets where they are absent, leveraging bank-based identity confirmation serves as a powerful alternative. To maintain trust during this handoff, you must narrate the journey within the user interface, clearly explaining why the redirect is happening and exactly what steps to expect.
When a user understands the legitimacy of the external link, the transition feels like a premium security feature rather than a suspicious detour, ensuring the security of mobile apps remains a competitive advantage rather than a barrier to entry. Such solution, implemented in Diagnostyka’s app which Miquido collaborated with, was appreciated by users, granting them both convenience and sense of security.
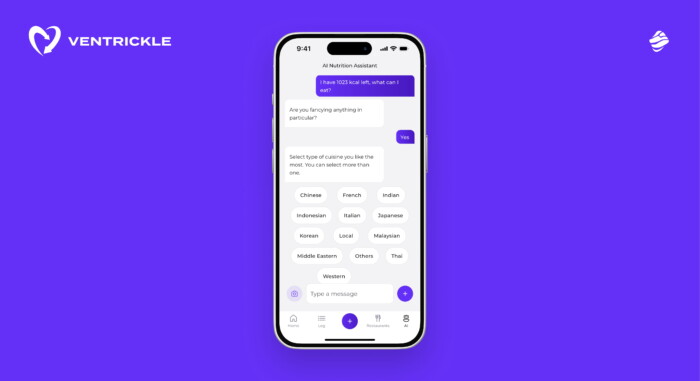
2. Implement robust AI guardrails for In-app assistants
Have you ever spent a few minutes experimenting with a built-in app chatbot, perhaps asking it to solve a complex calculus problem or provide a recipe for pancakes? To your surprise, many of them will eagerly comply.
While this might seem like a harmless quirk to a casual user, for a founder or a product owner, it represents a significant vulnerability. Such a "bug" often signals a lack of control over the underlying model, potentially masking deeper flaws in authentication and authorization that could eventually compromise your proprietary data or user safety.
Integrating a Large Language Model (LLM) into your product is only half the battle; the more critical half is containment. Relying on "wishful prompting" – simply telling the bot to be nice – is not a viable security strategy.
Without a dedicated architecture, your assistant can inadvertently leak trade secrets, expose sensitive customer data, or rack up astronomical token bills by answering queries that have nothing to do with your business. A bot that wanders off-mission isn't just a technical glitch; it’s a liability that can erode the hard-earned trust of your professional user base.
Establishing an independent verification layer for model integrity
The solution is to deploy a robust Guardrails layer designed to intercept both incoming prompts and outgoing completions. This layer acts as a sophisticated filter, ensuring the chatbot remains strictly within its professional domain and refuses to engage with malicious or irrelevant inputs.
By securing the AI interaction, you protect your brand integrity and ensure the assistant remains a reliable, helpful tool. A secure bot proves to your users that your R\&D team prioritizes safety at every touchpoint, turning a potential point of failure into a hallmark of a professional-grade product.
3. Deployment of runtime application self-protection (RASP)
Imagine a user downloads your FinTech app onto a device that, unknown to them, has been "jailbroken" or compromised by a background screen-recorder. From the moment they log in, your app is essentially performing on a compromised stage where every keystroke is being watched.
As a founder, you can’t control the user’s phone, but you can control how your app reacts to its environment. This is where the shift from passive security to active self-defense becomes critical. In an era where "vapor" apps – malware that evolves after installation – are becoming more sophisticated, your application must essentially act as its own digital bodyguard.
By implementing Runtime Application Self-Protection (RASP), your product gains the ability to monitor its own execution. It can detect in real-time if a debugger is attached, if the device has been rooted, or if malicious "hooking" frameworks are attempting to intercept your code’s logic.
This level of security of mobile apps ensures that the software doesn’t just rely on the operating system’s perimeter but actively hunts for threats within its own memory space. It transforms the app from a static target into a dynamic, self-aware entity that can shut down sensitive processes the moment a breach is detected.
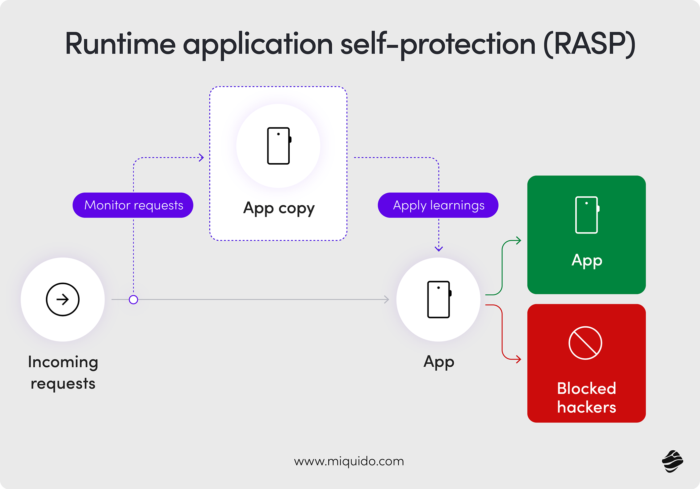
Transforming technical friction into a "safety shield" user experience
However, security shouldn't be a "black box" that leaves the user confused. Instead of a cryptic error message or a sudden crash that leads to a support ticket, use these moments to build brand authority.
A "Safety Shield" dashboard can inform the user that their environment is currently insecure – perhaps due to an outdated OS or a risky system setting – and provide clear, actionable steps to fix it. This approach turns a potential point of frustration into a moment of education, proving to your customers that you are looking out for their safety even when they aren't.
4. Defend the physical layer: NFC & Bluetooth resilience
Have you ever stood in a crowded subway or a busy coffee shop and felt a phantom vibration from your phone, only to realize nothing happened? While usually harmless, the rise of "NFC relay" scams and "WhisperPair" Bluetooth exploits means that physical proximity is the new frontier for hackers.
It’s no longer enough to secure the cloud; you must secure the two inches of air between a user’s phone and a terminal. For products that handle physical interactions – like digital keys or contactless payments – the physical layer is often the weakest link in the authentication and authorization chain.
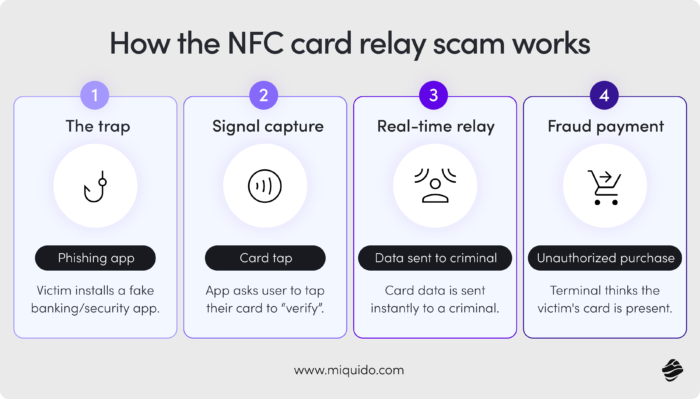
To combat this, security must be tied to intent. Requiring biometric re-authentication for every single NFC transmission ensures that a transaction can’t be "relayed" from a pocketed phone without the user’s explicit consent.
By leveraging cryptographic keys stored within the device’s Secure Enclave to sign these proximity-based transactions, you create a hardware-backed seal of approval. This ensures that even if a signal is intercepted, the underlying "secret" remains trapped in the silicon, making the stolen data useless to an attacker.
Providing clear "contextual alerts" during pairing or payment will ensure the user knows exactly which device they are interacting with.
5. Compiled UI over web-views for sensitive workflows
Think back to the last time you used a mobile app that felt "web-like" – perhaps the payment screen felt a bit sluggish or the fonts looked slightly off. While using Web-Views (embedded browsers) is a fast way to ship features, it opens a massive backdoor for "Man-in-the-Browser" attacks. In these scenarios, malware injects malicious scripts into the HTML page to silently modify a transaction or scrape credentials before they ever hit your server.
For an R\&D team, choosing the wrong rendering engine can inadvertently compromise the application security verification standard you’ve worked so hard to maintain.
The strategic move for sensitive workflows, such as account settings or wire transfers, is to move toward a Compiled UI approach. Frameworks like Flutter, using the Skia or Impeller engines, do not render standard HTML/DOM elements that a browser-based virus can easily manipulate.
Instead, they compile directly to native machine code and draw their own interface pixel-by-pixel. Because the UI is "baked in" and not interpreted on the fly like a website, it is inherently more resilient to traditional web-injection scripts and DOM-manipulation malware that target standard mobile browsers.
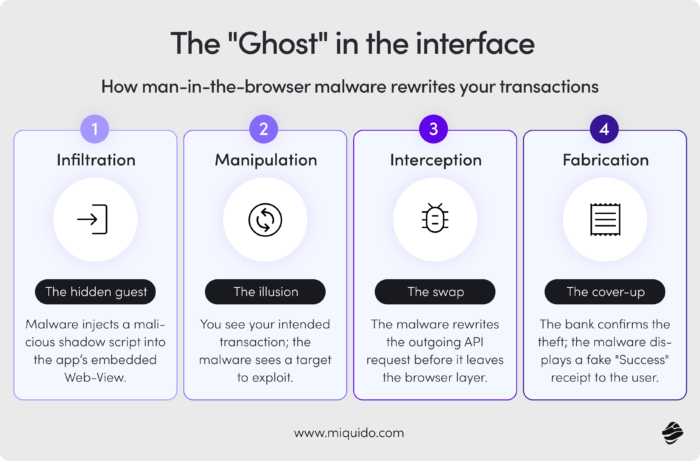
Bridging cross-platform agility with hardened native architecture
To truly harden this architecture, you should leverage specialized plugins that bypass the standard web layers entirely to interact directly with the underlying OS security modules. By implementing certificate pinning and network security protocols that run on the native side of the bridge, you create a dedicated, tamper-proof channel between your app and the server.
This bypasses the inherent vulnerabilities of the mobile browser environment, ensuring that your most critical business logic remains shielded from the chaotic "wild west" of web-based exploits.
6. Zero-trust secure storage & encryption
Imagine your user loses their phone at a busy airport. In their mind, the device is gone, but in your mind as a founder, the real countdown begins. If your application stores session tokens or personal profiles in plain text, that lost hardware is a wide-open door to your backend.
The most resilient products operate on a "Zero-Trust" philosophy, treating the device's local storage as a potentially hostile environment. This is one of the most critical application security examples where local defense prevents a total system breach.
To mitigate this, sensitive data must never sit "naked" on the disk. By implementing robust data encryption using algorithms like $AES-256-GCM$ and anchoring cryptographic keys within the hardware-backed KeyChain or Keystore, you ensure that data "at rest" is just as shielded as data "in transit."
It is a foundational requirement of the mobile application security verification standard (MASVS), ensuring that even if the physical silicon is compromised, the information within remains an unreadable cipher.
Auditing the life cycle of local data
Privacy-first engineering requires more than a one-time setup; it demands a regular audit of security controls to prune unnecessary data. By strictly limiting what is stored locally and ensuring that every byte is encrypted, you transform a liability into a fortress.
This proactive stance on security for mobile applications means that even in the worst-case scenario of a lost device, your company's and your users' integrity remains intact.
7. Hardened code via obfuscation & integrity checks
Have you ever wondered how quickly a competitor or a malicious actor could "look under the hood" of your app? Without protection, your compiled code is often an open book, revealing the proprietary logic and structures that make your product unique. For an R\&D team, leaving code transparent is like handing out the blueprints to your vault. Hardening your code via advanced obfuscation turns your logic into a "black box," making reverse engineering a task so arduous that most attackers simply give up.
Beyond mere obfuscation, implementing binary checks allows the app to verify its own app integrity at runtime. If a hacker tries to "re-package" your app with malicious code, the system detects the mismatch and refuses to execute. This level of mobile application protection ensures that your intellectual property remains yours and that no "counterfeit" version of your product can be used to harvest user data.
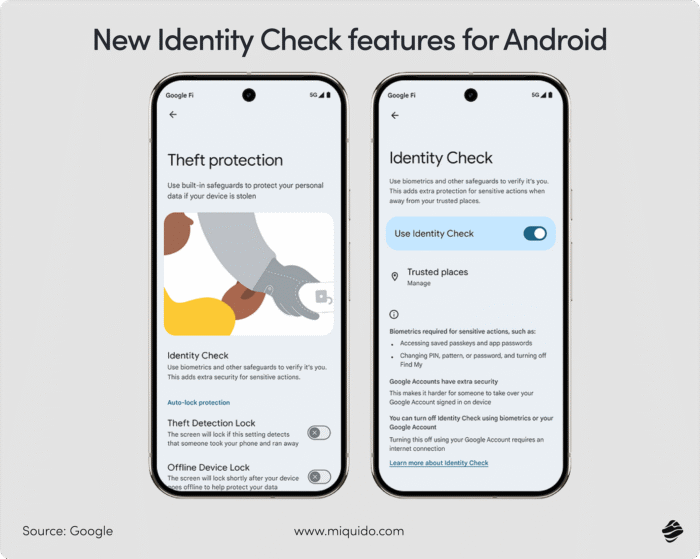
8. Adaptive multi-factor authentication (MFA)
We’ve all experienced the friction of waiting for an SMS code that never arrives – a classic "conversion killer." Modern secure authentication has evolved toward the elegance of Passkeys and device-bound biometrics. By shifting to hardware-attested security, you move away from the vulnerability of SIM-swapping and toward a world where the user’s physical device is the key. This transition aligns perfectly with the OWASP Mobile Security project goals of reducing reliance on phishable credentials.
Framing security as a "VIP" experience
When a user can log in with a seamless FaceID check, they don't feel "policed" – they feel recognized. This modern approach leverages the phone's Secure Enclave to provide a login experience that is significantly faster and exponentially more secure than a password could ever be. By implementing these standards, you are essentially adopting the MASVS framework for identity, turning a security necessity into a premium user benefit.
9. Just-in-time permissions & data privacy
Privacy is no longer a legal constraint; it is a premium feature. The era of "God-mode" apps that demand access to your camera and contacts upon the first launch is over. Today’s users are sophisticated and wary of "permission creep." Adopting the principle of least privilege – asking for permissions only at the exact moment they are needed – is a core tenant of the OWASP Mobile Application Security Verification Standard.
For features like document uploads, the mobile advantage lies in using system-level "File Pickers." This allows the user to grant your app access to one specific file without handing over their entire gallery. This "Just-in-Time" strategy ensures your app feels respectful, fostering a relationship where the user feels in control. Furthermore, by ensuring that these interactions are backed by secure communication protocols (like TLS pinning), you guarantee that the data travels safely from the user's hand to your vault.
10. Proactive security lifecycle & responsible disclosure
Security is not a destination; it is a living, breathing process. Even the most hardened apps can develop vulnerabilities as new exploits emerge. This is why a proactive security lifecycle, involving continuous API security testing and manual penetration testing, is non-negotiable. Following the OWASP Mobile guidelines for a secure software development lifecycle (SDLC) ensures that security is baked into every sprint, not bolted on at the end.
The vision: building a hardened community
By establishing a "Responsible Disclosure" policy, you provide a professional channel for "White Hat" hackers to report vulnerabilities directly to your R\&D team. This prevents bugs from being leaked on social media and turns potential adversaries into allies. Aligning your internal policies with the OWASP MASVS and maintaining rigorous session management protocols demonstrates to your board and users that you take their safety seriously. It transforms security from a back-office technicality into a core pillar of your company's brand promise.
Conclusion: Security as a brand advantage
In 2026, the most successful apps won't be the ones that simply "have a chatbot" or "allow a checkout" –they will be the ones that make the user feel safe through every scan, login, and conversation.

![[header] mobile app security best practices 10 essential tips for 2026](https://www.miquido.com/wp-content/uploads/2026/03/header-mobile-app-security-best-practices-10-essential-tips-for-2026-1920x1280.jpg)

![[header] mobile app security best practices 10 essential tips for 2026](https://www.miquido.com/wp-content/uploads/2026/03/header-mobile-app-security-best-practices-10-essential-tips-for-2026-432x288.jpg)
![[header] top 5 use cases for autonomous delivery in foodtech today](https://www.miquido.com/wp-content/uploads/2025/08/header-top-5-use-cases-for-autonomous-delivery-in-foodtech-today-432x288.jpg)

